Keep Updated with the Cloud Services Press Release: Trends and Advancements
Keep Updated with the Cloud Services Press Release: Trends and Advancements
Blog Article
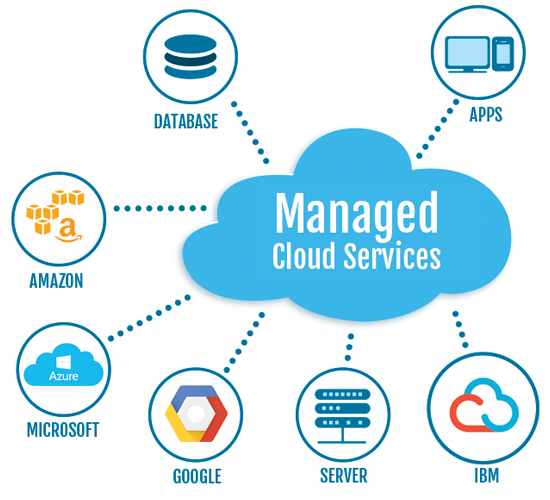
Secure and Reliable Information Administration Through Cloud Services
In the ever-evolving landscape of information management, the use of cloud solutions has become an essential remedy for businesses seeking to strengthen their information safety and security actions while enhancing functional efficiencies. universal cloud Service. The complex interplay between guarding delicate info and making sure seamless accessibility positions a facility challenge that organizations must navigate with diligence. By discovering the subtleties of secure information management via cloud services, a much deeper understanding of the approaches and modern technologies underpinning this paradigm change can be unveiled, losing light on the multifaceted benefits and considerations that form the modern data monitoring ecological community
Relevance of Cloud Providers for Data Administration
Cloud solutions play a critical role in modern-day information administration techniques due to their accessibility, cost-effectiveness, and scalability. Furthermore, cloud services give high accessibility, allowing users to gain access to information from anywhere with a web connection.
In addition, cloud services supply cost-effectiveness by eliminating the demand for spending in expensive equipment and maintenance. Organizations can go with subscription-based designs that line up with their budget and pay just for the resources they use. This aids in reducing upfront prices and total operational costs, making cloud services a viable choice for organizations of all dimensions. Fundamentally, the significance of cloud solutions in data administration can not be overstated, as they give the needed tools to streamline procedures, boost partnership, and drive service growth.
Secret Safety Obstacles in Cloud Data Storage Space

To resolve these protection difficulties, companies require durable security measures, including encryption, access controls, routine security audits, and personnel training. Partnering with relied on cloud provider that provide innovative protection functions and conformity qualifications can also help alleviate dangers linked with cloud information storage space. Inevitably, a positive and extensive strategy to safety and security is essential in protecting information kept in the cloud.
Implementing Information Encryption in Cloud Solutions
Carrying out data security in cloud options includes utilizing robust security algorithms and secure vital management techniques. Encryption tricks ought to be stored individually from the encrypted data to include an added layer of protection. Furthermore, organizations have to frequently upgrade security tricks and use solid accessibility controls to limit who can decrypt the data.
Additionally, data encryption need to be used not just throughout storage however additionally throughout data transmission to and from the cloud. Safe and secure communication procedures like SSL/TLS can aid guard information in transportation, making sure end-to-end file encryption. By focusing on data file encryption in cloud services, companies can bolster their data security pose and maintain the discretion and stability of their delicate information.
Ideal Practices for Data Backup and Recovery

Additionally, carrying out normal recuperation drills is necessary to evaluate the performance of backup procedures and the organization's capability to bring back information swiftly. Automation of back-up processes can streamline procedures and minimize the capacity for human error. Encryption of backed-up information includes useful link an added layer of security, securing sensitive information from unapproved accessibility throughout storage and transmission. By complying with these ideal techniques, services can enhance their data resilience and ensure smooth operations when faced with unanticipated events.
Surveillance and Bookkeeping Data Gain Access To in Cloud
To maintain data integrity and protection within cloud environments, it is necessary for organizations to develop durable measures for tracking and auditing information access. Monitoring data our website gain access to includes tracking that accesses the data, when they do so, and what activities they perform. By implementing surveillance mechanisms, organizations can discover any unauthorized gain access to or uncommon tasks promptly, allowing them to take prompt activity to alleviate prospective threats. Bookkeeping information gain access to goes an action additionally by providing an in-depth record of all information gain access to activities. This audit route is critical for compliance functions, investigations, and identifying any type of patterns of suspicious behavior. Cloud company commonly provide devices and services that assist in tracking and bookkeeping of data accessibility, permitting organizations to get insights right into just how their information is being made use of and ensuring accountability. universal cloud Service. By proactively checking and auditing information access in the cloud, companies can enhance their total protection posture and keep control over their sensitive information.
Final Thought
To conclude, cloud solutions play an important role in making certain safe and secure and reliable information management for services. By resolving crucial safety obstacles with information security, back-up, recuperation, and keeping track of methods, organizations can protect delicate details from unauthorized gain access to and data violations. Executing these best techniques in cloud services promotes information stability, privacy, and accessibility, inevitably enhancing cooperation and performance within the company.
The vital protection challenges in cloud data storage space revolve around information violations, data loss, conformity guidelines, and information residency issues. By encrypting data before it is uploaded to the cloud, organizations can minimize the danger of unauthorized gain access to and information violations. By prioritizing information security in cloud remedies, companies can bolster their data security pose and maintain the privacy and integrity of their delicate details.
To keep data honesty and protection within cloud atmospheres, it is vital for companies to develop durable procedures for monitoring and auditing information accessibility. useful source Cloud service providers typically provide devices and solutions that promote tracking and auditing of data accessibility, enabling organizations to gain understandings right into exactly how their information is being used and guaranteeing accountability.
Report this page